Intro:
We will use a custom resource written in Python that will be able to create ACM certificates with DNS validation. The custom resource will also automatically validate this certificate if the validation domain is managed by a Route53 hosted zone. We will also be able to specify an AWS region to create the certificate in, this region is independent of the Cloudformation stack region which for example makes it possible to deploy a certificate in region us-east-1 (to use with cloudfront) while deploying the stack in region eu-west-1. The resource will also provide the certificate arn as an output parameter so it can be used by other resources in the stack. Lastly when you delete the custom resource it will cleanup all validation records and the certificate itself.
Requirements:
- Python3
- Pip
- Bash
- Zip
- An S3 bucket to deploy the custom resource package on
- A hosted zone for the validation record
Implementation:
Let’s get started by downloading all the required code from our GitHub repository.
Step1: Uploading the custom resource package
In this step we are going to prepare the custom resource package and upload it to an S3 bucket.
First we go into the custom resource directory.
cd cloudar-acm-plus-custom-resource
Next we execute a script to install all required dependencies.
sh install_dependencies
Now we are ready to create the package.
sh pack_custom_resource

You will now find the zipfile ‘cloudar-acm-plus-custom-resource.zip’ in ‘cloudar-acm-plus-custom-resource/packed’, upload this zip file to your S3 bucket.
Step2: Creating a Cloudformation template
Now we can create a Cloudformation template in which we use this custom resource to create an ACM certificate.
You can use the template ‘cfn.yaml’ as an example.
First create a Lambda resource as following

Use the name of your bucket for the property ‘S3Bucket’ .
Next we create the custom resource.
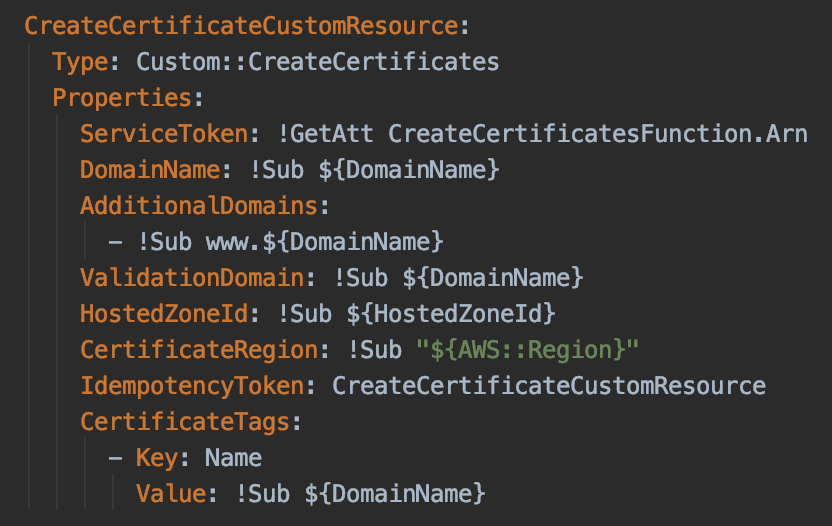
We can set the following properties here:
- DomainName: (REQUIRED type:String) The domain name for the acm certificate.
- AdditionalDomains: (OPTIONAL type:List) Additional domains for the acm certificate
- ValidationDomain: (REQUIRED type:string) The domain name for the validation domain of the acm certificate
- HostedZoneId: (REQUIRED type:string) The hosted zone id for the validation domain of the acm certificate
- CertificateRegion: (REQUIRED type:string) The region to deploy the acm certificate in
- IdempotencyToken: (REQUIRED type:string pattern: \w+) The idempotency token for the create call of the acm certificate doc: https://docs.aws.amazon.com/acm/latest/APIReference/API_RequestCertificate.html#ACM-RequestCertificate-request-IdempotencyToken
- CertificateTags: (OPTIONAL type:list) The tags for the acm certificate
In order for the DNS record cleanup and delete certificate functionality to work when you delete the Cloudformation stack it is important to set the following output.
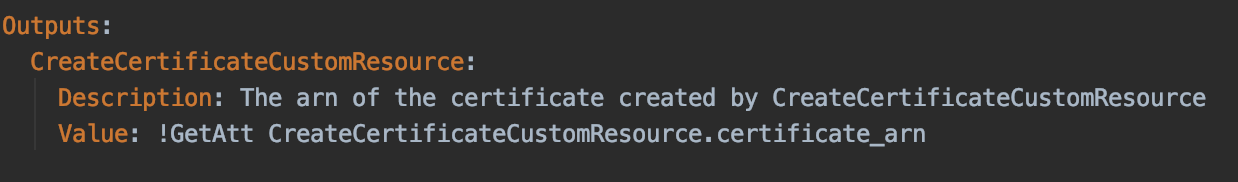
As you can see we can access the arn of the certifcate created by the custom resource with the GetAtt function on the resource.
!GetAtt CreateCertificateCustomResource.certificate_arn
Step3: Deploy the cloudformation
Finally the only thing left to do is deploy the Cloudformation template.
Once the deploy is started Cloudformation will create the Lambda containing the code from step1 and start a custom resource which will create the certificate and validation records. Once the status of the certificate becomes ‘ISSUED’ the custom resource will finish successfully and report the arn of the certificate back to Cloudformation. We can now further use this arn in other resources in the Cloudformation template.
When you delete the Cloudformation stack, the custom resource will cleanup the validation records in the hosted zone and delete the certificate.
CREATE_COMPLETE
![]()


